Database Security Audit
Secure Your Databases from the Inside Out
Protect your critical data from insider threats, breaches and sophisticated attacks. Our comprehensive Database Security Audit identifies, quantifies and reduces risk across your SQL Server and Oracle environments.
DataWyse helps you regain control and build confidence in your database security posture. Our audit provides clear visibility and actionable plans to safeguard your most sensitive information.
Benefits
Clear Risk Visibility
Gain a high-level snapshot of database security risks across your entire estate. Understand where your most critical vulnerabilities lie with an executive-ready risk heatmap and prioritised findings.
Actionable Remediation Roadmaps
Move beyond identified risks with a practical, implementation-ready remediation plan. We provide a sequenced roadmap focused on reducing the most risk with the greatest efficiency, aligning security efforts with business objectives.
Enhanced Compliance and Audit Readiness
Demonstrate alignment with key security frameworks like CIS Controls and ISO/IEC 27001. Our evidence-based reporting supports audit requirements and ensures your database security measures stand up to scrutiny.
Strengthened Resilience and Recovery
Reduce the impact of ransomware or destructive attacks by securing backup integrity and validating restore readiness. We help you establish robust controls to protect against data loss and ensure business continuity.
Optimised Security Investments
Focus your security spend where it matters most. Our audit prioritises risks, enabling you to invest in solutions that deliver the greatest reduction in exposure and provide the best return on investment
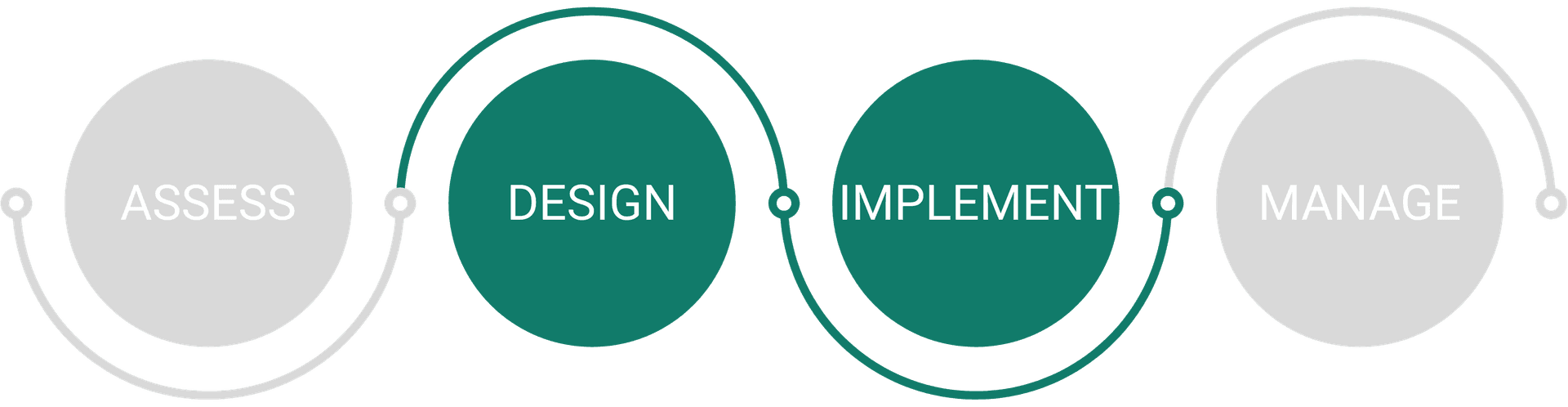
How it Works
Step1: Rapid Risk Snapshot
We begin with a high-level assessment of your database estate to quickly identify key security control gaps. This phase includes discovery, initial risk scoring and a prioritised heatmap, giving you a top-down view of potential vulnerabilities and recommended targets for deeper review.
Step 2: Deep Dive Technical Audit
For your highest-risk systems, we conduct a detailed technical audit. This involves in-depth evidence collection and validation of controls across privileged access, secure configurations, auditing and patch hygiene. You receive an implementation-ready remediation plan for immediate action.e.
Step 3: Focused Encryption Review
We perform a dedicated review of your encryption controls for data at rest, in transit and in backups. This includes assessing key management practices to ensure your data protection measures are robust and effective, providing an uplift plan and configuration standards.
Who It's For
The DataWyse Database Security Audit is ideal for mid-market to corporate organisations using Microsoft data technologies or hybrid data environments. This includes businesses with critical workloads, sensitive or regulated data and those facing limited internal DBA or security capacity. If you need to simplify complexity, reduce operational risk and accelerate your journey toward a secure, compliant and AI-ready data environment, our service is for you.
Frequently Asked Questions
What database platforms do you support?
We cover SQL Server (on-premise, IaaS, Azure SQL MI/DB) and Oracle (on-premise, IaaS, RDS for Oracle where applicable). Our assessments are tailored to the specific nuances of each platform.
How is this different from a penetration test?
Our service is a security audit, focusing on identifying configuration weaknesses, access control issues and governance gaps within the database itself. It does not involve active exploit development or penetration testing, which typically falls outside this scope unless separately requested.
What kind of access is required?
We primarily require read-only access to your database environments such as to metadata and configuration views. This minimises disruption and ensures a non-invasive assessment process. For certain deep-dive activities, additional access may be required and will be clearly communicated.
How long does an audit take?
The duration depends on the size and complexity of your database estate and the chosen engagement phases. A Phase 1 risk snapshot can be completed relatively quickly to provide fast visibility while a full three-phase engagement covering detailed audits and encryption reviews will take longer. We provide a detailed project timeline during the scoping process.
Will you help us fix the identified issues?
The Database Security Audit focuses on identifying risks and providing a detailed remediation roadmap. Implementation of these recommendations falls outside the scope of this audit but can be provided as a follow-on engagement through our Technical Services team.
Ready to Strengthen Your Database Security?
Take control of your data security posture today. Contact us for a detailed assessment and safeguard your critical assets.